Consensus Mechanisms are an absolute core concept in mining, maintenance and security of the blockchain. Let’s see what are they and their mission.

What is the role of the Consensus Mechanisms?
Consensus mechanisms exist because they are vital to maintaining the agreement, trust, and security of any decentralized computer network.
And because the blockchains where cryptocurrencies run are a decentralized network – they do not rely on validation from a central entity – there needs to be a decentralized consensus formula.
These mechanisms, which are nothing more than complex algorithms, are the heart of any modern, functional and reliable blockchain.
Attempts to create virtual money in the 1980s and 1990s almost always ended up failing because a solution to keep the blockchain self-sustained in a decentralized way was never achieved.
This major difficulty was finally overcome in 2008 with the creation of the software that enabled the birth of Bitcoin.
When the pseudonymous Satoshi Nakamoto created the first cryptocurrency (the Bitcoin) so that it would not be dependent on third parties and would remain decentralized, he created a consensus mechanism called Proof of Work, which we will discuss below.
Currently, the consensus mechanisms that exist have to be, among others:
- efficient
- fair
- able to operate in real-time
- functional
- reliable
- secure
- fault-tolerant
- decentralized
- self-sufficient
- self-regulating
It’s a lot of things, isn’t it? That’s why it was a very complicated problem to solve.
Which Consensus Mechanisms Exist?
There are several and different types of consensus algorithms, each of them works on different principles. Here we will review some of the most important ones.
Proof of Work (PoW):
This was the first of them all, launched with Bitcoin. It is still the best known and is still the one used in major currencies such as Bitcoin or Ethereum (but this may change in the near future).
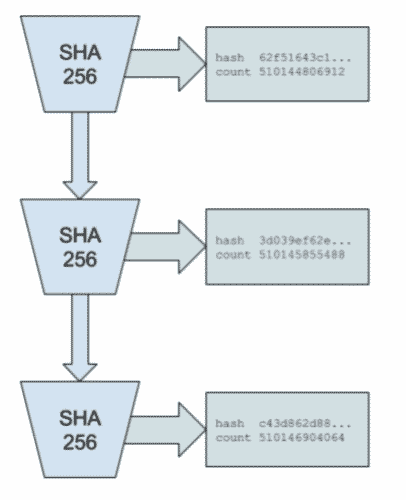
In this system, “miners” compete with each other to solve advanced mathematical puzzles based on cryptography so that the new block being added to the network is confirmed and legitimate.
The “miners” are nodes that perform the PoW calculation, and the new block will always have the hash of the previous block. To be able to change the chain history, you would need to change all the existing blocks.

When it comes to blockchains that use PoW, a 51% attack explains that the attacker can gain control of more than 51% of the hash. If it can do that, the attacker is able to manipulate the data on that blockchain.
But being able to gain control of more than 51% in an established network with thousands of nodes is practically impossible, not to mention the immeasurable amount of energy to do so.
This model is the subject of much criticism due to its environmental impact, as it requires an extreme amount of computing power.
The Bitcoin mining process consumes about 91 terawatt-hours of electricity annually, which is almost the same as several countries in the world, such as Austria with almost 9 million inhabitants.
Another major criticism of the PoW system is its poor performance, as it can process few operations at the same time.
As an example, the Bitcoin network only processes about 7 transactions per second. To get an idea, VISA’s network can process about 1,700 per second.
Currently Ethereum still runs in a Proof of Work format, but there are plans afoot to change to the Proof of Stake (PoS) system which we will cover below. This change is planned for 2022.
Proof of Stake (PoS):
Proof of Stake is the mechanism for the latest generation coins that are gaining immense market share. These are the cases of Cardano (ADA), Polygon (MATIC), Polkadot (DOT), Algorand (ALGO), among others.
It has come to be seen as the alternative to PoW for having a lower cost in transactions, consuming much less energy and having a much better performance.
The way in which the consensus algorithm works is different from PoW. Here there is no mining, nor is there a reward for mining.
If, in Bitcoin, there is the reward for the first one who verifies/adds a new block, here in PoS, whoever contributes (called a forger or minter) earns a transfer fee.
The algorithm selects the participants who have the highest amount of staked (reserved) coins as validators, assuming that the highest stakeholders are incentivized to ensure a transaction is processed.
The idea is that those with the most coins in circulation have the most to lose, so they are positioned to work in the interest of the network.
In order to have the ability to validate transactions on the network, the user will have to place their coins in a wallet (or specific area within it). This wallet ‘freezes’ the coins, meaning that they cannot be moved while they are being used to support the network.
Have no fear that there will be the ability to withdraw/use them should you need to.

As you may have already understood, in this example you need to have the coins to participate in the maintenance and validation of the network. Here an initial coin investment is required.
Let’s take an example, used one of the most mediatized coins of recent months: Cardano (ADA).
Anyone who owns Cardano can stake and become a validator node. When Cardano needs to verify blocks, its Ouroboros protocol selects a validator. The validator checks the block, adds it, and gets more Cardano for his work.
However, if a validator proposes to add a block with incorrect or malicious information, it will lose all its stake value as a penalty.
Note that within the PoS format, the protocols that validators choose can vary greatly.
This is why most participants join staking pools. The owner of a staking pool creates the validator node, and a group of people pool their coins for a better chance of winning new blocks.
The rewards are divided among the participants of the pool according to the amount of coins you have set aside. The owner of the staking pool can also earn a small fee.
This is a form of passive income called staking and described in detail in the article.
These being, the two most common consensus mechanisms today, there is a strong discussion between both, with their pros and cons, so let’s put both in the table below.
| Proof-of-Work (PoW) | Proof-of-Stake (PoS) |
| Mining is determined by how much computational work is done by the miner | The probability of validating a new block is determined by the amount of coins owned (in staking) |
| A reward is awarded to the first miner who solves the demanding cryptographic problem of each block | You are not given a reward for mining, but a fee from the network |
| The network of miners competes with each other using extreme computers and power power | Immensely lower energy cost, although there is still some doubts because they are relatively new |
| Malicious users need to being able to gain control of more than 51 per cent of the hashing power, in order to revert all the entire network history | Malicious users need to have 51% of all currency in stake on the network to make a 51% attack |
Delegated Proof-of-Stake (DPoS):
Delegated Proof of Stake is a variation (some call it an evolution) of the PoS explained above.
Here, network users vote and elect delegates to validate the next block. The delegates are also called witnesses. Using DPoS, you can vote for delegates by collecting your coins in a staking pool, which is connected to a particular delegate. You do not physically transfer your coins to another wallet, but use a service provider for this.
For each new block a limited number of delegates are chosen (most protocols choose between 20 and 100), so the delegates in one block may not be the delegates in the next block.
The elected delegates receive the transaction fees of the validated block, and that reward is then shared with the users who have reserved their coins in the successful delegate’s staking pool. The more that is staked, the greater the share of the block reward that is received.
Being a direct evolution of PoS, it also allows for cheaper transactions, greater scalability, and excellent energy efficiency.
It is also considered a more democratic way of choosing who validates the next block, but because of this it is partially centralized, which is a disadvantage.
Some of the coins that use this algorithm are EOS or BitShares.
Proof-of-History (PoH):
Proof-of-History, to date is used in only one coin: Solana (SOL). But since it is not just any coin, and Solana is a global scale blochcain with tremendous potential, this is one of the consensus mechanisms that will also be addressed.
With this mechanism, instead of relying on the time stamp of the transaction, you are going to prove that the transaction occurred before and after an event.
PoH is a high frequency Verifiable Delay Function. A Verifiable Delay Function requires a specific number of sequential steps to evaluate, but produces a unique result that can be efficiently and publicly verified.
This protocol differs from the current pattern of blockchains infrastructure that we have been talking about in that it does not rely on a sequential production of blocks that are delayed by waiting for confirmation across the network before moving forward.
To some experts, PoH represents a fundamental advance in the structure of networks with respect to speed and capacity.
Proof of Capacity (PoC):
Here, miners use computer storage instead of the more common Proof of Work (PoW) mining method, which involves permanent computational operations and consumes much more energy.
Like others, this format emerged with a focus on combating the absurd energy consumption of the PoW system.
The PoC protocol comprises of a two-step process that involves first allotment and then mining.
PoC allows mining devices, also known as nodes, on the network, to use the empty space on their hard drives to mine the available cryptocurrencies.
Instead of repeatedly changing the numbers in the block header and repeating the hash for the solution value as in a PoW system, PoC works by storing a list of possible solutions on the mining device’s hard drive, even before mining activity begins.
The larger the hard disk, the more possible solution values can be stored on the hard disk, the more chances a miner has to match the required hash value of his list, resulting in more chances to earn the mining reward.
Any disk can be used, including Android-based systems.
There is no need for dedicated (and usually expensive) hardware or to be upgrading your disks constantly, as the data used can be easily erased to use again.
There is not a huge adoption of this method, to date. Some of the coins that use it are Chia, Burst and Storj.
Consensus Mechanisms: Conclusion
At the core of any blockchain is one such consensus mechanisms.
Consensus algorithms allow network participants to agree on the contents of a blockchain in a distributed way and without having to rely on a tertiary or centralized entity.

Don’t think we’ve covered them all, as there are a few dozen and their variations, but we’ve certainly covered the current major consensus mechanisms.
Although the Proof of Work and Proof of Stake protocols are the ones that currently dominate, it is worth remembering that all this technology is still ‘green’ and we will still see many improvements and updates.
We may have consensus mechanisms that have not even been created yet and will dominate the cryptocurrencies of the future.
